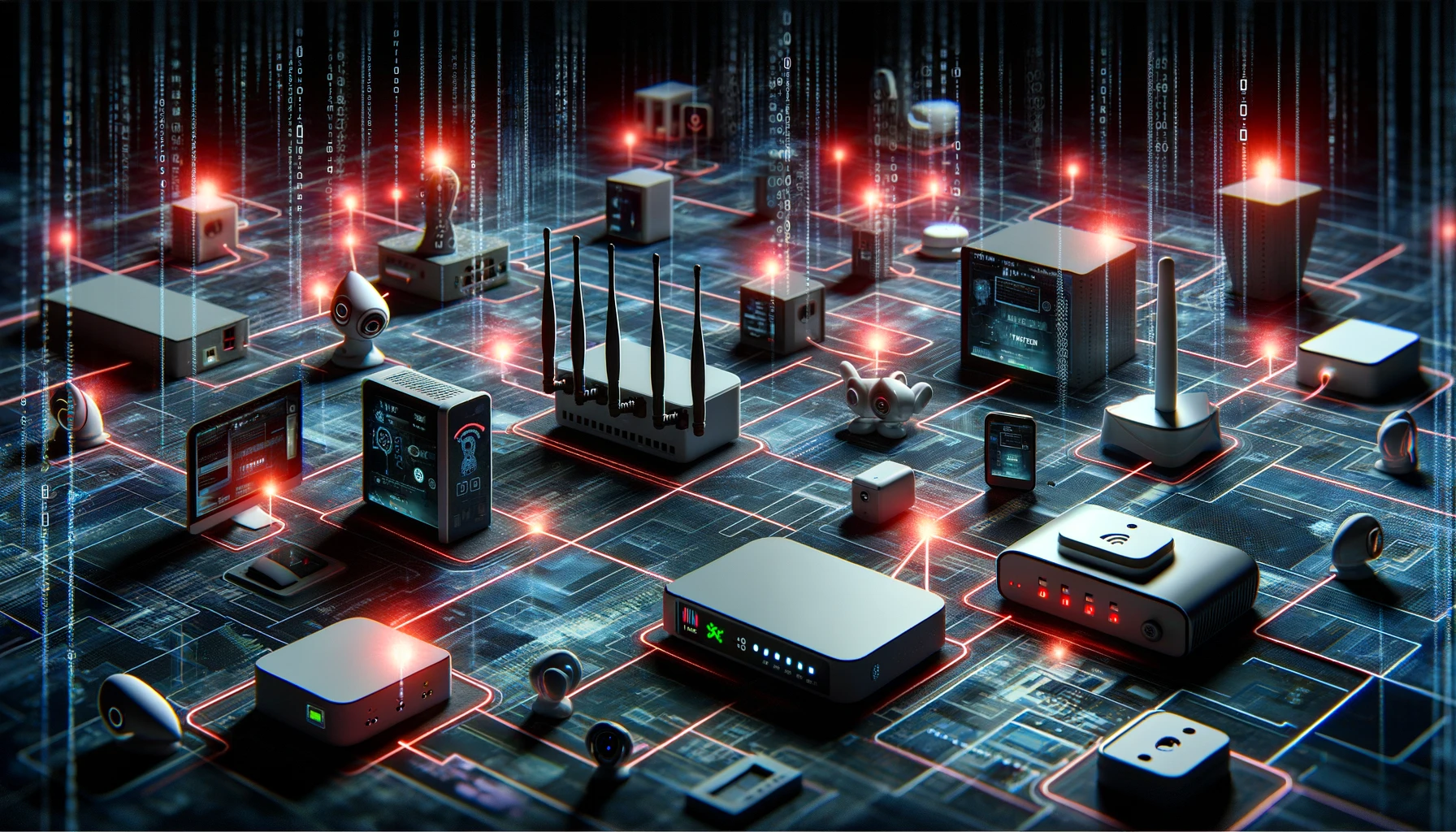
In a significant development reported by Akamai’s Security Intelligence Response Team (SIRT) in late October 2023, heightened malicious activity was detected, indicating the exploitation of zero-day vulnerabilities to disseminate a variant of the Mirai botnet, named ‘InfectedSlurs’. This botnet specifically targets Network Video Recorders (NVRs) and outlet-based wireless LAN routers commonly used in hotels and residences. The attackers exploit these vulnerabilities for remote code execution (RCE), inducting infected devices into a DDoS swarm.
Akamai’s Research Findings:
- Mirai Botnet Expansion: The Mirai botnet is known for orchestrating large-scale DDoS attacks by controlling a wide array of connected IoT devices.
- TCP Port Vulnerabilities: Akamai’s research highlighted probes targeting a rarely used TCP port, pointing towards a zero-day exploit in NVR devices.
- Specific Device Targeting: The botnet focuses on particular NVRs and wireless LAN routers. The NVR manufacturer has acknowledged this zero-day exploit and is expected to release a fix by December 2023. Additional details about the second zero-day affecting wireless LAN routers are also anticipated soon.
Technical Details and Indicators of Compromise (IOCs):
- Malware SHA256SUMs: Various samples of the malware, adapted for different architectures, have been linked to the botnet. The SHA256SUMs of these samples are vital for detecting compromised systems.
- C2 Infrastructure: The botnet leverages distinct C2 domains and IP addresses. Notable domains include ‘iaxtpa[.]parody’ and ‘infectedchink[.]cat’. The infrastructure exhibits synchronized changes and unusual domain resolutions.
Acknowledgement:
This report is based on the findings and research conducted by Akamai’s Security Intelligence Response Team (SIRT). Their proactive detection and analysis of these zero-day vulnerabilities have been instrumental in understanding the expanding threat landscape posed by the Mirai botnet.